Many security problems start for homes, businesses and government when no one is watching. Video surveillance services from 5163co assure monitoring around the clock and from all angles to keep an eye on places you value, even when you are not looking. Security and video surveillance systems, known as closed-circuit television (CCTV), consist of a camera, digital video recorder (DVR), and monitor. 5163co and Access offers a large variety of high-quality equipment to bring you cutting-edge solutions.

CLOSED CIRCUIT TELEVISION

INTERCOM SYSTEMS

AUDIO INTERCOMS

AUDIO / VIDEO (AV) INTERCOMS
ALARM SYSTEMS


PHONE ENTRY INTERCOMS
IP INTERCOMS

MONITORING
SENSORS

CONTROLLERS
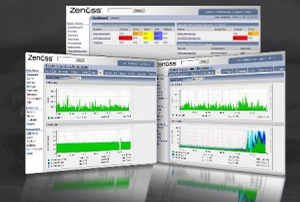
REPORTS

ELECTRONIC LOCKS

KEYPAD LOCKS
HOTEL LOCKS

Locks are synonymous with the hotel industry, where the security of guests nd their personal property is always at a premium. The quality and reliability of locks can make or break a hotel brand, which is why the lodging business turns to 5163co. and Access for superior selection, installation and maintenance.
BIOMETRIC LOCKS

Biometric locks utilize the uniqueness of human body features to offer convenience and enhanced security in residences, businesses and government installations. These keyless locks predominantly make use of fingerprint scanning technology, and sometimes retinal scanning, iris scanning and voiceprint identification.
MAGNETIC STRIP LOCKS

Magnetic strip locks operate with plastic keycards identical in size to a credit card or driver’s license. They are popular in areas where different users must be accommodated without having to change the lock each time, such as in hotels or small businesses.
ELECTRIC STRIKE LOCKS
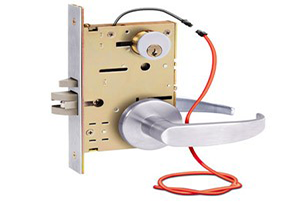
Electric strikes, also known as door strikes or door releases, are used in locations where access control is required. Many people are familiar with electric strikes for the “buzz-in” sound made when the current flows through the electric strike to open a door. Integrated Security Systems Integrated security systems are one of the latest developments in closed-circuit television systems (CCTV) design. These systems available from 5163co. and Access offer an overall security solution that is easy to use, which makes them increasingly popular for small business owners and small offices.
Customers interested in CCTV choose integrated security systems because they involve simple hook ups and basic user interfaces. The systems consist of a digital video recorder (DVR), a display monitor and a network card. Integrated security systems look like an LCD monitor, and in fact they can be used strictly for that purpose, but their compact size makes them appealing for many people who need a CCTV solution for security and video surveillance. Integrated security systems provide a flexible and reliable storage option. The DVR component can record up to 14 days of footage using high-resolution recording. A USB outlet allows the recordings to be moved to a USB key or external hard drive for later transfer to a DVD. Although one never wants to experience a crime, if something does happen, the ability to copy recordings is essential for police investigations, which require a copy of the recording. The built-in network card in an integrated security system allows users to connect remotely from the internet and see what their cameras are viewing at any time. This feature is particularly helpful for small business owners and home-office owners who travel. All that is needed for peace of mind is a computer and an internet connection. Compact size, flexibility and convenience make integrated security systems an attractive, state-of-the-art security solution. Consider a system from vertex security for your home office or small business today
ACCESS MANAGEMENT AND CONTROL (ACS)

How can people have freedom to come and go without compromising the security of an area? Access management and control answers this question by letting you determine who can enter and exit an area, and what level of access they will have inside. Advanced access control systems like keypad alarm systems and biometric readers bring many advantages over traditional locks and keys. These newer systems allow a manager to lock and unlock doors automatically, for example, and to track and document which individuals went where, and when. That information is highly valuable if the need arises to review and investigate a security incident. Access control systems (ACS) can be integrated into a comprehensive security plan that involves aspects of physical layout like heating and cooling systems, electronic locks, closed circuit television, and security surveillance. While access control and management provide peace of mind to homeowners, due to their sophistication, these systems are more often used in government installations and high-profile commercial targets such as banks, hotels and some apartment complexes. Laboratory and testing areas that store sensitive items like radioactive materials and other top-secret devices use access control systems, including remote access control and thumb print readers. Businesses that work with sensitive government contracts also generally are required to have these systems in place. 5163co.. offers state-of-the-art access control systems and components including keypad alarm systems, biometrics, and card access. Which system you choose depends on what the purpose will be.
KEYPAD ACCESS
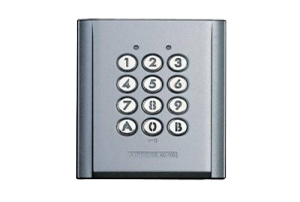
A keypad alarm system is a basic alarm system with a low-voltage circuit that involves sensors on doors and windows. When a window or door is opened, the electricity through the sensor is interrupted and the alarm will sound if activated unless a code is typed into the security keypad. Some of these alarms also use motion sensors and are triggered when motion is detected inside an area. Keypad alarms, which are available in wired or wireless types, offer several advantages over other alarm systems. They allow the user to control all the access points in a structure, giving access only to select people. These alarms also can be activated whether or not the user is in the area. Wired keypad alarm systems connect to a control panel. The wires, hidden in walls and various crawl spaces, go to sensors placed on doors and windows, and the keypads themselves. Instead of wires, wireless keypad alarm systems use radio transmitters to send signals to each other. The same alarm effect is created when doors or windows are opened without entering the code into the numeric keypad.
BIOMETRICS

The term “biometrics” comes from the Greek words “bios” meaning life and “metron” meaning measurement. Biometrics is the science of confirming a person’s identity through the analysis of that individual’s unique physical or behavioral traits. In access control, biometric systems can include fingerprint-readers and voice and retina-recognition systems. These solutions offer advantages over other keyless methods like card readers, which can be lost or stolen. In contrast, biometric systems grant access based on unique traits that cannot be easily lost, such as fingerprints, vocal sounds and retinas. These traits also are not easily duplicated by anyone seeking to tamper with the security system
CARD ACCESS
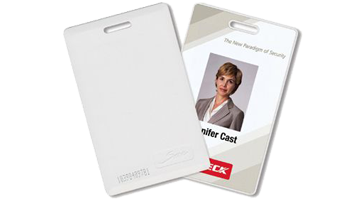
Card access relies on keycards, normally flat and rectangular-shaped pieces of plastic, that are presented to a card reader. Access control card readers are used in physical security systems to read a credential that allows access through controlled points, often a locked door. Access control readers offered by 5163co. are classified by functions they are able to perform and by identification technology. Types include a magnetic stripe, bar code, smart card, and proximity cards.
MAGNETIC STRIP
Magnetic stripe technology uses a stripe of magnetic oxide tape laminated on a keycard card. Three tracks of data, which can be encoded in any format, are on the magnetic stripe. Mag-stripe cards, as they are called, are inexpensive and easy to program and use. On the down side, the technology is susceptible to misreads, card wear, data corruption, and copying.
BARCODE
Barcode technology uses a series of alternating dark and light stripes that are read by an optical scanner. The organization and width of the lines is determined by the bar code protocol chosen. Bar codes are inexpensive and easy to generate, but this also makes them susceptible to fraud, and smudges and dirt may cause problems with the reader.
SMART CARD

Smart cards come in two types: contact and contactless. Both have an embedded microprocessor and memory that can handle multiple applications and allow the smart card to work as a cash card, a pre-paid membership card, and an access control card. The difference between contact and contactless smart cards is how their microprocessors communicate. A contact smart card has eight contacts that must physically touch the right points on the card reader, which makes them slow and undesirable for most access control purposes, which require speed of transaction. A contactless smart card uses the same radio-based technology as the proximity card but with a higher frequency that allows for transfer of more data and communication with several cards at a time. Contactless cards do not have to touch the reader and remain in a wallet or purse, which makes them a better choice for access control systems. The cards usually do not use the available memory for access control, which frees the memory for uses like biometrics data.
PROXIMITY CARD
Many companies use proximity cards to control physical access. In this system, an employee holds a card within a few inches of the reader; the reader receives a unique ID from the card and transmits it to a central computer that commands whether or not to open the door. A primary reason for the popularity of proximity cards is the convenience of their touch-less functionality. One drawback to proximity cards is the increasing number of cards manufactured with no governing body to control card numbers and facility codes, key parts of their operating format. Different manufacturers could supply cards with identical facility codes and control numbers to different organizations, which causes a problem of duplicates. Now more than ever, commercial and government clients need fast, reliable telecommunications and data services to connect within their units and among external parties. A solid telecom and data infrastructure is essential to the smooth operations of businesses, safe transmission of sensitive government messages, and overall peace of mind. 5163co. specializes in low voltage, infrastructure cabling, audio/video, telecom and data solutions that improve the way you communicate and do business. Our experts stay on top of developments in this swift-moving area to bring you state-of-the-art designs and the latest equipment for your needs.